Back
Psoda features
All features
Aggregation
Easily transform project data into powerful programme and portfolio views.
Workflows
Unleash the full potential of your productivity by automating your custom workflows.
Reporting
Experience the power of interactive, customisable reports tailored just for you.
Dashboards
View information exactly the way you desire with personalised dashboards.
User access control
You have the power to define who can access what with Psoda’s advanced user access control.
Scenario planning
Say goodbye to guesswork and hello to informed decision-making with real-time scenarios.
Automations
Streamline your work with smart automations and focus on what really matters.
Integrations
Supercharge your productivity. Seamlessly integrate with your other business tools.
Back
Psoda solutions
Strategic portfolio management
Identify, prioritise, balance and deliver your initiatives.
Programme management excellence
Plan, monitor and control your programs.
Project management simplified
Schedule, manage and execute your projects.
PMO success
Make informed decisions, accurately report and effectively govern.
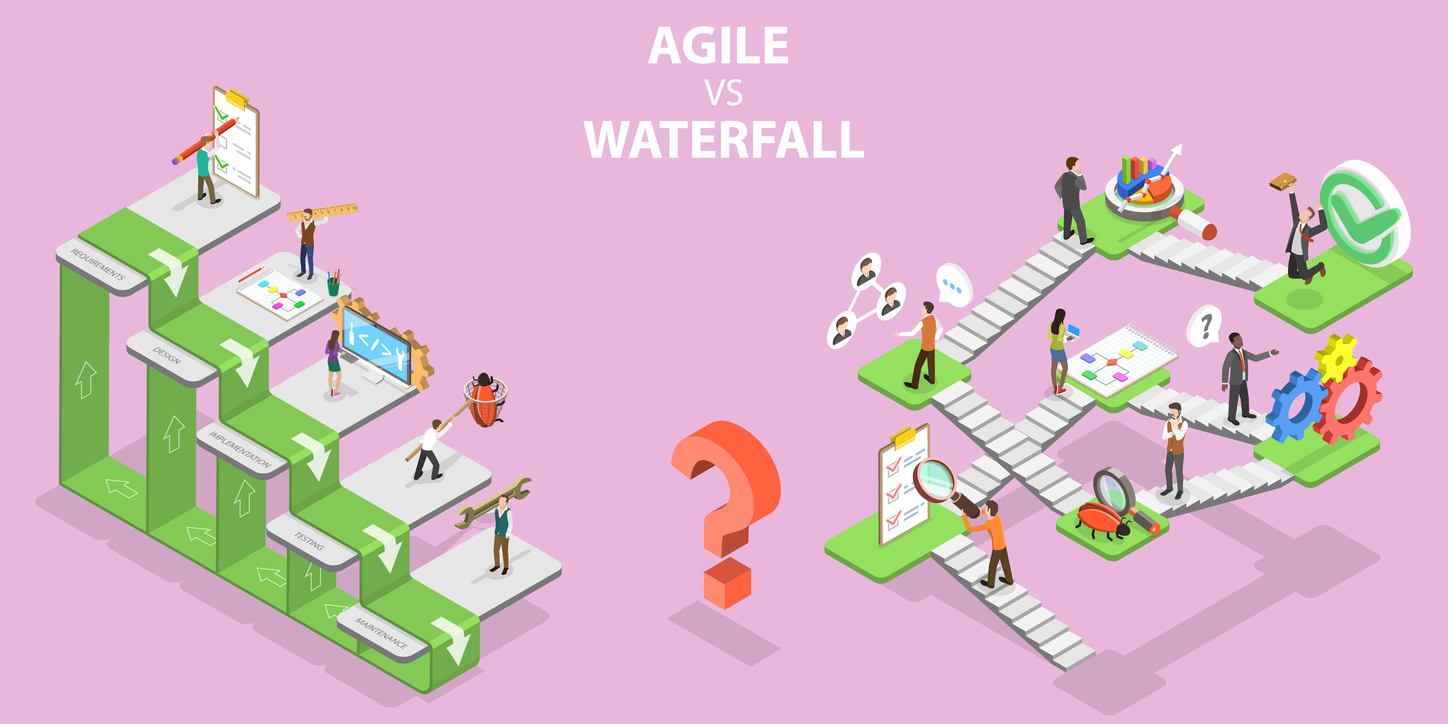
Scaled agile
Support business agility and agile planning through full SAFe practices.
Back
Why Psoda?

See it for yourself
We offer a FREE one hour personalised live demo of Psoda run by our CEO Bruce Aylward.
Schedule a demo
Back
Psoda
Case studies
All case studies
Contact Energy case study
Contact realises centralised consolidation of project information and gains time-savings.
Hamilton City Council case study
Improved project transparency enables Hamilton City Council to take the long view.
North Island University case study
North Island University delivers projects more successfully, efficiently and consistently with Psoda.
Te Whatu Ora case study
Transforming healthcare delivery: Te Whatu Ora Capital, Coast and Hutt Valley's journey with Psoda.
Latest blog post